E

Authenticity in Sales: Why it Matters - ESA
E

@Electronic Security Association
Electronic Security
Jan 29, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
1Posts
1Sources
0Reputation
Latest signal
0 reactions
Authenticity in Sales: Why it Matters - ESA
esaweb.org
0Following
0Comments
0Views
0Shares
E

Going in-depth on the Windows 10 random number generation infrastructure | Microsoft Securi...
E

@Enterprise & Security Team
Enterprise &
Jan 28, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
1Posts
1Sources
0Reputation
Latest signal
0 reactions
Going in-depth on the Windows 10 random number generation infrastructure | Microsoft Security Blog
microsoft.com
0Following
0Comments
0Views
0Shares
E
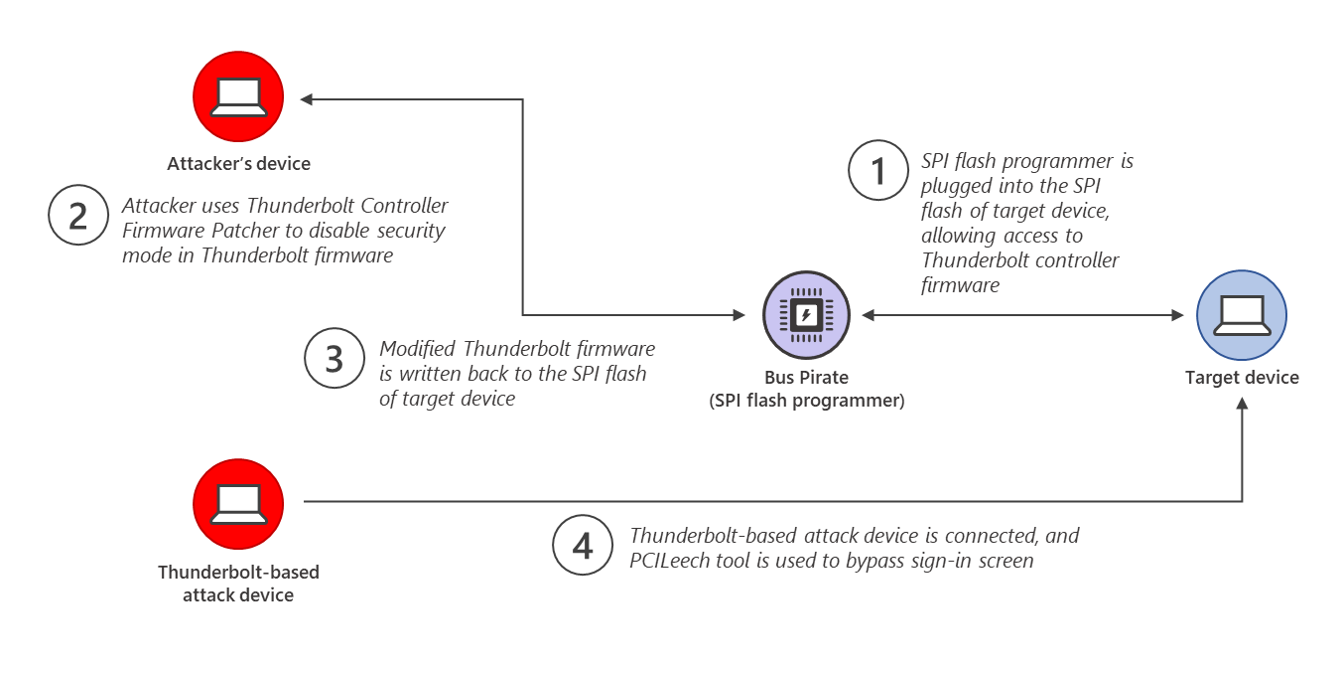
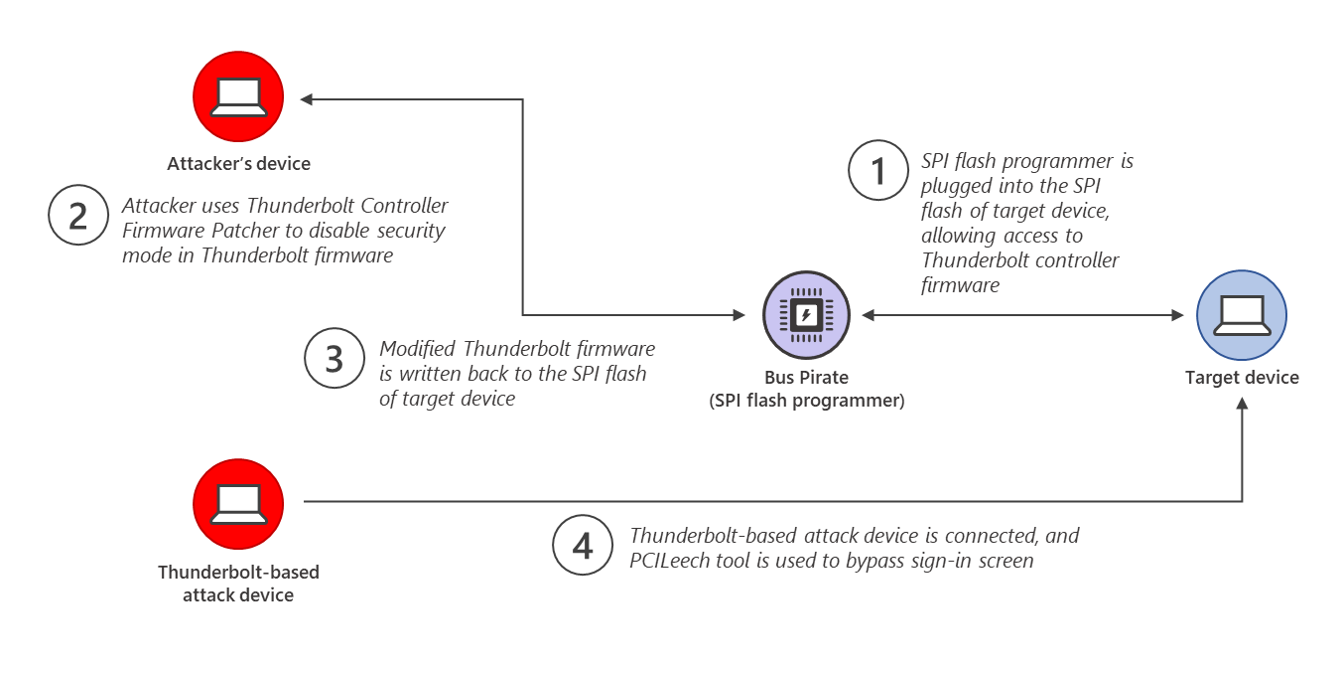
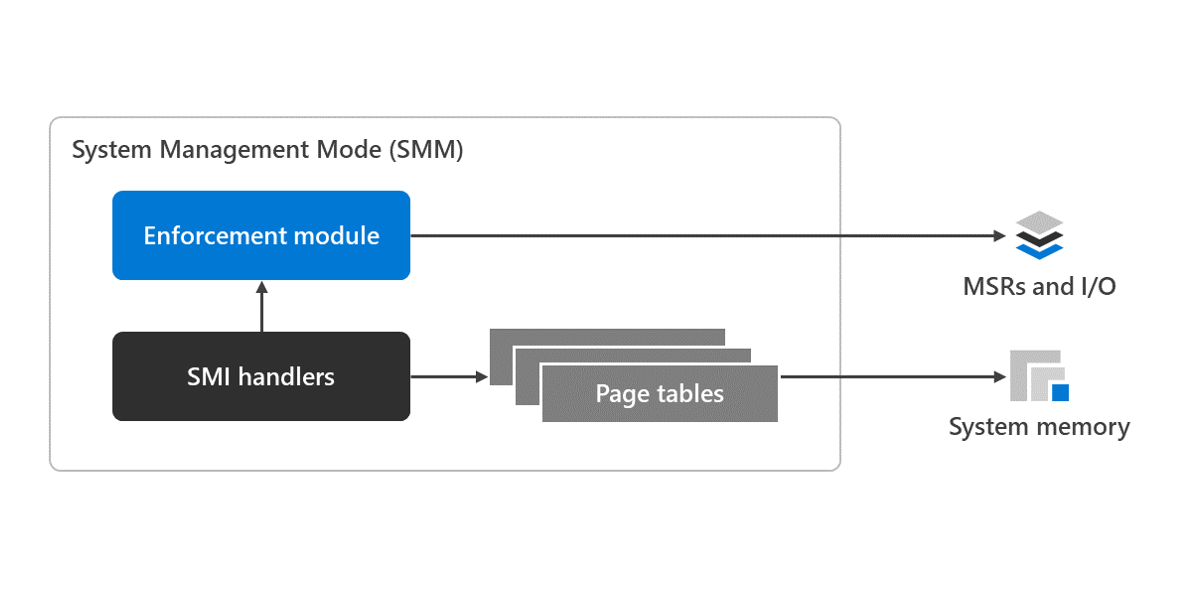
Secured-core PCs help customers stay ahead of advanced data theft | Microsoft Security Blog
E

@Enterprise and OS Security
Enterprise And
Feb 7, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
6Posts
1Sources
0Reputation
Latest signal
0 reactions
Secured-core PCs help customers stay ahead of advanced data theft | Microsoft Security Blog
microsoft.com
0Following
0Comments
0Views
0Shares
E

3 steps to secure your multicloud and hybrid infrastructure with Azure Arc | Microsoft Secu...
E

@Enterprise and OS Security, Abhilash Kankanawadi
Enterprise And
Feb 7, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
1Posts
1Sources
0Reputation
Latest signal
0 reactions
3 steps to secure your multicloud and hybrid infrastructure with Azure Arc | Microsoft Security Blog
microsoft.com
0Following
0Comments
0Views
0Shares
E

SharePoint Under Siege: ToolShell Exploit (CVE-2025-49706 & CVE-2025-49704) - Eye Research
E

@Eye Security
Eye Security
Jan 27, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
1Posts
1Sources
0Reputation
Latest signal
0 reactions
SharePoint Under Siege: ToolShell Exploit (CVE-2025-49706 & CVE-2025-49704) - Eye Research
research.eye.security
0Following
0Comments
0Views
0Shares
F

2026年もソフトウェアサプライチェーンのリスクに立ち向かうために...
F

@flatt_security
Flatt_security User
Mar 26, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
2Posts
1Sources
0Reputation
Latest signal
0 reactions
2026年もソフトウェアサプライチェーンのリスクに立ち向かうために / Product Security Square...
speakerdeck.com
0Following
0Comments
0Views
0Shares
The Foundation for Energy Security and Innovation (FESI) Announces Investments to Defend Am...
F

@Foundation for Energy Security and Innovation (FESI)
Foundation For
Feb 27, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
1Posts
1Sources
0Reputation
Latest signal
0 reactions
The Foundation for Energy Security and Innovation (FESI) Announces Investments to Defend America's Critical Infrastru...
prnewswire.com
0Following
0Comments
0Views
0Shares
F

In journalist security field, maturing and understanding - Committee to Protect Journalists
F

@Frank Smyth/CPJ Journalist Security Coordinator
Frank Smyth/CPJ
Jan 29, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
1Posts
1Sources
0Reputation
Latest signal
0 reactions
In journalist security field, maturing and understanding - Committee to Protect Journalists
cpj.org
0Following
0Comments
0Views
0Shares
F

Knowing how law and technology meet at US borders - Committee to Protect Journalists
F

@Frank Smyth/CPJ Senior Adviser for Journalist Security
Frank Smyth/CPJ
Feb 7, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
1Posts
1Sources
0Reputation
Latest signal
0 reactions
Knowing how law and technology meet at US borders - Committee to Protect Journalists
cpj.org
0Following
0Comments
0Views
0Shares
G

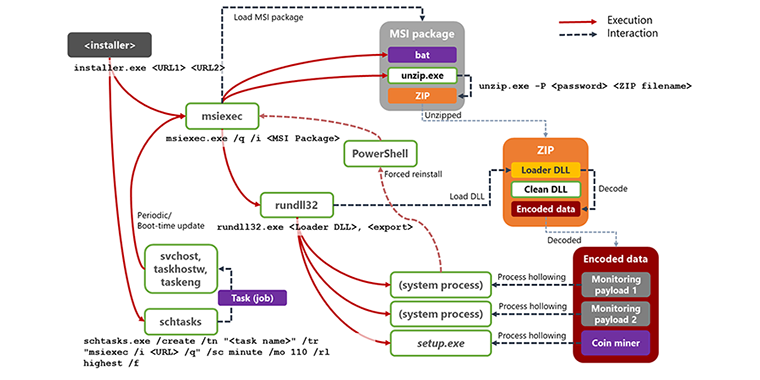
Digging Gold with a Spoon – Resurgence of Monero-mining Malware
G

@G DATA Security Center
G DATA
Apr 30, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
1Posts
1Sources
0Reputation
Latest signal
0 reactions
Digging Gold with a Spoon – Resurgence of Monero-mining Malware
blog.gdatasoftware.com
0Following
0Comments
0Views
0Shares
G

Exploring GenAI in Cybersecurity: Gemini for Malware Analysis
G

@G DATA Security Lab
G DATA
Feb 2, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
6Posts
1Sources
0Reputation
Latest signal
0 reactions
Exploring GenAI in Cybersecurity: Gemini for Malware Analysis
gdatasoftware.com
0Following
0Comments
0Views
0Shares
G

how to remove MyCouponsmart on macOS |
G

@geeksecurity1
Geeksecurity1 User
Jan 24, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
1Posts
1Sources
0Reputation
Latest signal
0 reactions
how to remove MyCouponsmart on macOS |
applehelpwriter.com
0Following
0Comments
0Views
0Shares
GNSI Tampa Summit Series
G

@Global and National Security Institute
Global And
Apr 26, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
1Posts
1Sources
0Reputation
Latest signal
0 reactions
GNSI Tampa Summit Series
usf.edu
0Following
0Comments
0Views
0Shares
G

allemand – Global Security Mag Online
G

@Global Security Mag Online
Global Security
Feb 1, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
4Posts
2Sources
0Reputation
Latest signal
0 reactions
allemand – Global Security Mag Online
globalsecuritymag.de
0Following
0Comments
0Views
0Shares
G

GuidePoint Security researcher discovers vulnerability in the integrity of common HMI clien...
G

@GuidePoint Security
GuidePoint Security
Jan 24, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
3Posts
1Sources
0Reputation
Latest signal
0 reactions
GuidePoint Security researcher discovers vulnerability in the integrity of common HMI client-server protocol | GuideP...
guidepointsecurity.com
0Following
0Comments
0Views
0Shares
H

Wi-Fi honeypots: Alive and well at RSAC 2018 - Help Net Security
H

@Help Net Security
Help Net
Apr 20, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
65Posts
3Sources
0Reputation
Latest signal
0 reactions
Wi-Fi honeypots: Alive and well at RSAC 2018 - Help Net Security
helpnetsecurity.com
0Following
0Comments
0Views
0Shares
H

Statistics on spam, phishing, viruses, ransomware, and advertising
H

@Hornetsecurity
Hornetsecurity User
Feb 3, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
3Posts
1Sources
0Reputation
Latest signal
0 reactions
Statistics on spam, phishing, viruses, ransomware, and advertising
hornetsecurity.com
0Following
0Comments
0Views
0Shares
H

Forrester Study Recommends Zero Trust Approach to Endpoint Security to Reduce Attack Surfac...
H

@HP Wolf Security
HP Wolf
Apr 19, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
2Posts
1Sources
0Reputation
Latest signal
0 reactions
Forrester Study Recommends Zero Trust Approach to Endpoint Security to Reduce Attack Surface and Improve Productivity...
threatresearch.ext.hp.com
0Following
0Comments
0Views
0Shares
H

WordPress Security for High Performance Websites - MalCare
H

@http://twitter.com/malcaresecurity
Http://twitter.com/malcaresecurity User
Jan 23, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
1Posts
1Sources
0Reputation
Latest signal
0 reactions
WordPress Security for High Performance Websites - MalCare
malcare.com
0Following
0Comments
0Views
0Shares
The Cost of September 11
I

@IAGS, Institute for the Analysis of Global Security
IAGS, Institute
Jan 29, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
1Posts
1Sources
0Reputation
Latest signal
0 reactions
The Cost of September 11
iags.org
0Following
0Comments
0Views
0Shares
I

SPS-Verschlüsselung von Siemens SIMATIC S7-1200/1500 ist angreifbar
I

@Infopoint Security, Munich, Germany
Infopoint Security,
Feb 1, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
1Posts
1Sources
0Reputation
Latest signal
0 reactions
SPS-Verschlüsselung von Siemens SIMATIC S7-1200/1500 ist angreifbar
infopoint-security.de
0Following
0Comments
0Views
0Shares
I

Data Security Guide | Information Security
I

@Information Security
Information Security
Feb 5, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
1Posts
1Sources
0Reputation
Latest signal
0 reactions
Data Security Guide | Information Security
security.duke.edu
0Following
0Comments
0Views
0Shares
I
I

@Infosecurity Magazine News Team
Infosecurity
No posts yet
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
0Posts
0Sources
0Reputation
Latest signal
0 reactions
No indexed post preview available yet.
Discovery profile
0Following
0Comments
0Views
0Shares
I

Intego's New Total Protection | One solution for Mac Protection
I

@IntegoSecurity
IntegoSecurity User
Jan 27, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
2Posts
2Sources
0Reputation
Latest signal
0 reactions
Intego's New Total Protection | One solution for Mac Protection
intego.com
0Following
0Comments
0Views
0Shares
I

How to Defend Yourself Against NSO Spyware Like Pegasus
I

@Intercept Security Team
Intercept Security
Jan 27, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
1Posts
1Sources
0Reputation
Latest signal
0 reactions
How to Defend Yourself Against NSO Spyware Like Pegasus
theintercept.com
0Following
0Comments
0Views
0Shares
J
![[20230201] - Core - Improper access check in webservice endpoints](/media-proxy.php?url=https%3A%2F%2Fcdn.joomla.org%2Fimages%2Fsharing%2Fjoomla-org-og.jpg)
[20230201] - Core - Improper access check in webservice endpoints
J

@Joomla! Security Strike Team
Joomla! Security
Jan 23, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
3Posts
1Sources
0Reputation
Latest signal
0 reactions
[20230201] - Core - Improper access check in webservice endpoints
developer.joomla.org
0Following
0Comments
0Views
0Shares
J

Statement by Members of International Law Association Committee on Use of Force
J

@Just Security
Just Security
Feb 24, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
26Posts
2Sources
0Reputation
Latest signal
0 reactions
Statement by Members of International Law Association Committee on Use of Force
justsecurity.org
0Following
0Comments
0Views
0Shares
K

Kratos Defense & Security Solutions, Inc. Announces
K

@Kratos Defense & Security Solutions, Inc.
Kratos Defense
Apr 20, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
1Posts
1Sources
0Reputation
Latest signal
0 reactions
Kratos Defense & Security Solutions, Inc. Announces
globenewswire.com
0Following
0Comments
0Views
0Shares
L

NRA Law Enforcement Division | NRA Explore
L

@Law Enforcement, Military, Security
Law Enforcement,
Feb 12, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
4Posts
1Sources
0Reputation
Latest signal
0 reactions
NRA Law Enforcement Division | NRA Explore
le.nra.org
0Following
0Comments
0Views
0Shares
L

After TikTok: Navigating the Complex Web of Foreign Tech Bans - Security Boulevard
L

@Lohrmann on Cybersecurity
Lohrmann On
Feb 1, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
1Posts
1Sources
0Reputation
Latest signal
0 reactions
After TikTok: Navigating the Complex Web of Foreign Tech Bans - Security Boulevard
securityboulevard.com
0Following
0Comments
0Views
0Shares
M

XLM + AMSI: New runtime defense against Excel 4.0 macro malware | Microsoft Security Blog
M

@Microsoft 365 Security, Microsoft Threat Intelligence
Microsoft 365
Jan 29, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
2Posts
1Sources
0Reputation
Latest signal
0 reactions
XLM + AMSI: New runtime defense against Excel 4.0 macro malware | Microsoft Security Blog
microsoft.com
0Following
0Comments
0Views
0Shares
M

Keeping browsing experience in users' hands | Microsoft Security Blog
M

@Microsoft Defender Security Research Team
Microsoft Defender
Mar 28, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
32Posts
1Sources
0Reputation
Latest signal
0 reactions
Keeping browsing experience in users' hands | Microsoft Security Blog
microsoft.com
0Following
0Comments
0Views
0Shares
M

Training People on Threat Modeling | Microsoft Security Blog
M

@Microsoft Security
Microsoft Security
Feb 24, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
4Posts
1Sources
0Reputation
Latest signal
0 reactions
Training People on Threat Modeling | Microsoft Security Blog
microsoft.com
0Following
0Comments
0Views
0Shares
M

Recent enhancements for Microsoft Power Platform governance | Microsoft Security Blog
M

@Microsoft Security Team
Microsoft Security
Apr 12, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
41Posts
1Sources
0Reputation
Latest signal
0 reactions
Recent enhancements for Microsoft Power Platform governance | Microsoft Security Blog
microsoft.com
0Following
0Comments
0Views
0Shares
M

300 Billion Emails, Infinite Risk: Email Security Evolution
M

@Mike P | Return on Security
Mike P
Jan 27, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
1Posts
1Sources
0Reputation
Latest signal
0 reactions
300 Billion Emails, Infinite Risk: Email Security Evolution
returnonsecurity.com
0Following
0Comments
0Views
0Shares
M

How AI Is Changing the Way Yards Stop Cargo Theft - Supply Chain 24/7
M

@Milan Luketic, Birdseye Security Solutions
Milan Luketic,
Jan 29, 2026
Content creator and web explorer. Sharing discoveries from around the internet.
0Followers
1Posts
1Sources
0Reputation
Latest signal
0 reactions
How AI Is Changing the Way Yards Stop Cargo Theft - Supply Chain 24/7
supplychain247.com
0Following
0Comments
0Views
0Shares






























![[20230201] - Core - Improper access check in webservice endpoints](/media-proxy.php?url=https%3A%2F%2Fcdn.joomla.org%2Fimages%2Fsharing%2Fjoomla-org-og.jpg)